Blog

6 Ways to Combat Social Phishing Attacks
Phishing is the number one method of attack delivery for everything from ransomware to credential theft. We are very aware of it coming by email, but other types of phishing have been growing rapidly. In recent years, phishing over social media has skyrocketed by 500%. There has also been a 100% increase in fraudulent social …

4 Interesting Cloud Storage Trends to Watch for in 2022
One area of cloud computing that is used widely, but often isn’t as flashy as the software side is cloud storage. Storing files in the cloud to make them easily accessible and shareable from anywhere was one of the very first uses of the cloud that was adopted widely by many users. As advances like …

5 Things You Should Never Do on a Work Computer
Whether you work remotely or in an office, the line between personal and work tasks can become blurred when working on your company computer. If you’re in front of a computer for most of your time during work, then it’s not unusual to get attached to your desktop PC. Over time, this can lead to …

Alarming Phishing Attack Trends to Beware of in 2022
In 2020, 75% of companies around the world experienced a phishing attack. Phishing remains one of the biggest dangers to your business’s health and wellbeing because it’s the main delivery method for all types of cyberattacks. One phishing email can be responsible for a company succumbing to ransomware and having to face costly downtime. It …

Important Steps to Take Before You Recycle a Mobile Phone Number
It’s not unusual to change a mobile number from time to time. For example, when you move, you may want a number that is local to the area you just moved to. Companies also may end up recycling mobile numbers throughout their staff as people come and go. If you don’t properly detach your mobile …

These Google Search Tips Will Save You Tons of Time!
Over 2.4 million searches happen every minute on Google. It’s often the first stop people make when they go online. We search daily for both personal and work needs, and often searching out the right information can take a lot of time if you have to sift through several irrelevant results. One study by consulting …

Top 5 Cybersecurity Mistakes That Leave Your Data at Risk
The global damage of cybercrime has risen to an average of $11 million USD per minute, which is a cost of $190,000 each second. 60% of small and mid-sized companies that have a data breach end up closing their doors within six months because they can’t afford the costs. The costs of falling victim to …

What Are the Most Helpful Features of Windows 11?
Windows 11 has been out for a few months now, beginning rollout in October of 2021. It has been largely well-received and seen as stable with very few bugs noted. One of the reasons that Windows 11 has been welcomed with open arms for both home and business computer upgrades is that it isn’t a …

Lead Your Business More Effectively by Implementing Unified Communications
Unified communications are a go-to solution for business owners looking to streamline their businesses and increase employee productivity in the long term. See how it benefits your business. Providing high-quality communication channels is crucial for any company. After all, it promotes cross-department collaboration and faster exchange of ideas. Since phones often don’t suffice for this, …

Making Your VoIP Network Bulletproof (Six Tips to Protect Your VoIP from Cyberattacks)
Hardly any phone call system in a business beats VoIP when it comes to efficiency and flexibility. However, it’s not immune to cyberattacks. Discover how you can secure your VoIP ASAP. What kind of communication system are you using for your business? I asked because many modern-day businesses have now switched to the Voice Over …

The Critical Importance of Virtualized Infrastructure Security (And 4 Ways to Enhance It)
A torn-down virtual infrastructure creates risks for any business. And it can have a significant impact on how quickly you can retrieve your data and resume operations following an attack. These days, many businesses use virtualized infrastructure for more straightforward data storage. It’s because this approach is superior to physical solutions due to enhanced flexibility, …
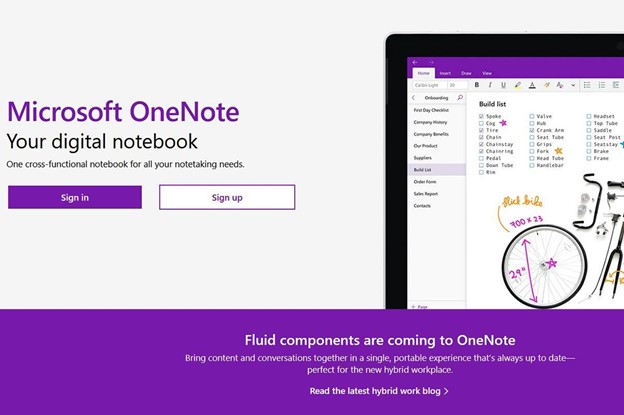
How OneNote Can Streamline Team Collaboration (And Four Tips to Make the Most of This Program)
OneNote is a digital note-taking tool that comes with plenty of benefits for users. But what you may not have realized yet is how powerful this app can be for enhancing team collaboration. Note-taking. This is an essential part of day-to-day operations for many business owners, managers, and teams. After all, people can’t rely on …